Analysts and investigators increasingly rely on unique identifiers rather than names when matching business records across public databases because identifiers cut false matches and speed verification.
In practice, a company ID appears in filings, registries and docket entries and becomes the backbone of a defensible company profile. This article explains what a company ID is, where it appears in public records, and how to use it for rigorous research and due diligence.
Relying on identifiers improves match rates and reduces manual review. Practitioners who start with an identifier trace filing histories, ownership links and compliance events more reliably than by name alone. The methods below assume access to public records sources and a disciplined capture of source, filing date and jurisdiction to preserve auditability and repeatability in research.
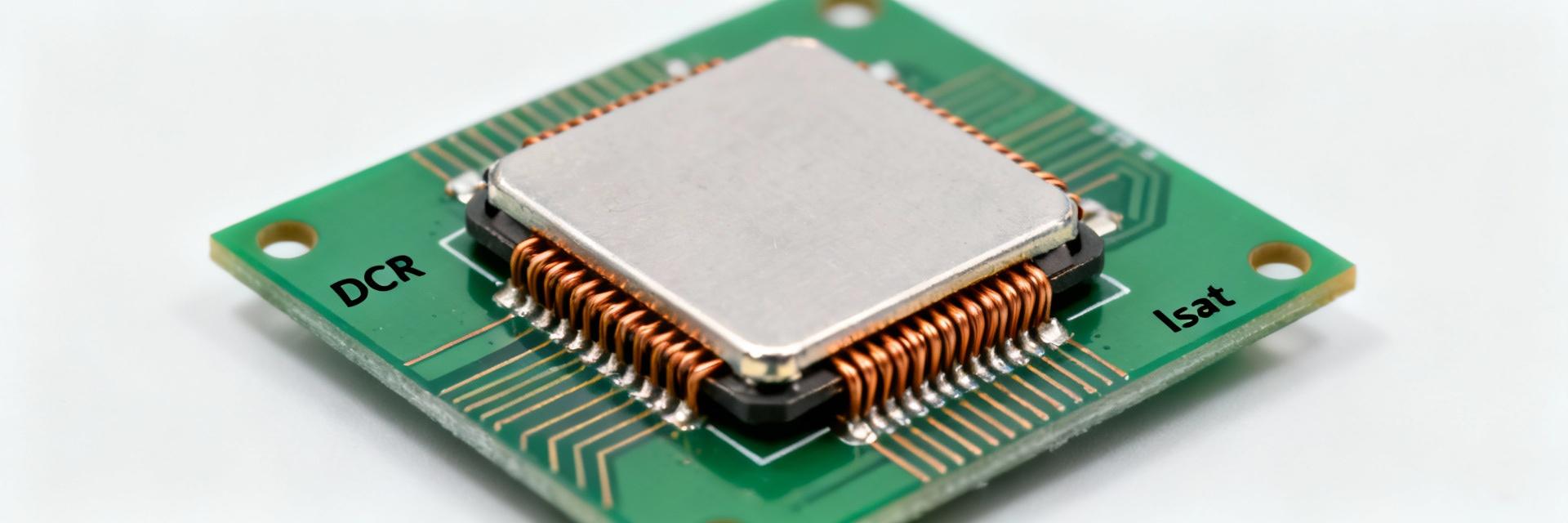
1 Background: What a Company ID Is and Why It Matters
Definition & common identifier types
Point: A company ID is a unique, persistent identifier assigned or recorded for a legal entity.
Evidence: Registries and tax authorities assign registration numbers, filing IDs and tax identifiers that travel with filings.
Explanation: These can be formatted as numeric strings, alphanumeric registry codes or jurisdictional filing numbers; capturing the exact string and issuing authority is essential to avoid conflating similarly named entities.
Why identifiers beat name-based searches
Point: Names are ambiguous; identifiers are precise.
Evidence: Trade names, transliteration differences and rebrands create false positives in name searches.
Explanation: An identifier ties disparate records—filings, liens, court dockets—back to a single entity, reducing false matches and surfacing cross-jurisdiction activity that name-only queries typically miss.
2 Data Analysis: Public Records That Reveal a Company ID
3 Method Guide: How to Locate and Validate a Company ID
Step-by-step search & verification workflow
Point: Use a prioritized workflow to find the authoritative ID.
Evidence: Start from a suspected name, locate the earliest official filing, extract the identifier and then cross-check across registries.
Explanation: Prioritize jurisdictional registries first, then securities or lien systems; use boolean queries for filing numbers and document types and always record source, filing date and URL/PDF metadata for provenance.
Common pitfalls, false positives & validation checks
Point: IDs can be misleading if unchecked.
Evidence: Reused numbers, parent/sub confusion and data-entry errors generate false links.
Explanation: Validate candidate IDs by matching registered addresses, agent names and officer records; inspect filing histories and request certified copies when critical—discrepancies in those elements are red flags requiring escalation.
4 Case Examples: What Public Records Can Reveal (anonymized)
Ownership, structure & linkage signals
Point: IDs reveal corporate relationships across filings.
Evidence: A single registry ID appearing in multiple jurisdictions or on group filings frequently signals parent-subsidiary relationships.
Explanation: Tracing ID reuse over time can show re-domiciles, mergers or the appearance of holding entities; anonymized traces often expose a control node linking otherwise unrelated operating names.
Financial & compliance signals from filings
Point: Filings tied by ID surface financial and compliance risks.
Evidence: UCC liens, repeated amendments, bankruptcy petitions and regulatory enforcement cases typically reference the same identifier.
Explanation: Flagging these signal types and quantifying frequency and recency improves risk scoring—multiple liens or enforcement actions tied to an ID raise escalation priority in due diligence.
5 Actionable Checklist: Building a Company Profile
Profile template: fields to collect and verify
Point: A concise schema standardizes collection.
Evidence: Core fields include canonical name(s), company ID(s), jurisdictions, filing history, beneficial owners, officers, addresses, licenses and lien history.
Explanation: Mark mandatory versus optional fields and cite each data point with record type, filing number and saved source (URL or PDF).
Compliance, privacy & documentation best practices
Point: Respect legal limits while maintaining auditable records.
Evidence: Combining public records with personal data can implicate privacy rules and data-use policies.
Explanation: Keep an audit trail—screenshots, PDFs and metadata—note the retrieval date and jurisdictional access rules to support regulatory compliance.
Summary
- A company ID is the most reliable bridge between disparate public records; capturing the exact identifier and issuing jurisdiction turns scattered filings into a defensible company profile for due diligence.
- Begin with the earliest official filing to extract the identifier, normalize formats across datasets and validate using addresses, registered agents and filing histories to reduce false positives.
- Track financial and compliance signals tied to the identifier—liens, amendments and enforcement actions—to quantify risk and prioritize escalation in investigative workflows.
Frequently Asked Questions
What is the quickest way to find a company ID from a name?
Begin at the jurisdictional business registry: search the corporate name, then open the earliest available filing to capture the registration or filing number. Cross-check that identifier in securities, UCC and court dockets to confirm consistency. Document the source and filing date for each match to preserve provenance and support later verification steps.
How can I validate a company ID found in public records?
Validate by corroborating the ID against multiple independent public records: registration entry, recent filings, officer lists and address matches. Review filing histories for continuity, check for successor or merged entities, and obtain certified copies for high-risk cases. Discrepancies between filings and registry entries are a strong prompt for escalation.
What does a company ID reveal about ownership and risk?
When properly traced, an identifier exposes ownership links, parent/sub relations and cross-jurisdiction registrations. It also aggregates risk indicators—liens, bankruptcies, enforcement actions—associated with the same legal entity. Using an ID-centric profile improves accuracy in ownership mapping and produces stronger, data-backed risk assessments for due diligence.